AD Database Hybrid
AD/Database User Source
This AD/Database Hybrid User Source is not manageable from within Ignition. Users/passwords must be administered through Active Directory, and roles, contact info, and so on, must be administered directly through the database. The way AD/Database Hybrid works, is it has all the same information requirements as the other authentication profiles, but it also has a number of Database properties. You need to specify a database (i.e., MySQL) to store information, and set up queries that you want to use. You must also specify the host that is acting as your primary domain controller, and a secondary domain controller in case the primary is unavailable. You'll also need to specify the name of the domain and credentials for the Gateway itself to use for authentication when it queries the list of roles.
AD/Database User Sources now support SASL (Simple Authentication and Security Layer). SASL is a framework for authentication and data security in Internet protocols such as LDAP.
Property Reference
This User Source shares many properties with both the AD User Source and Database User Source.
- See the Active Directory Authentication page for a list of Active Directory User Source related properties.
- See the Database Authentication page for a list of Database User Source related properties.
Creating an AD/Database Hybrid User Source
-
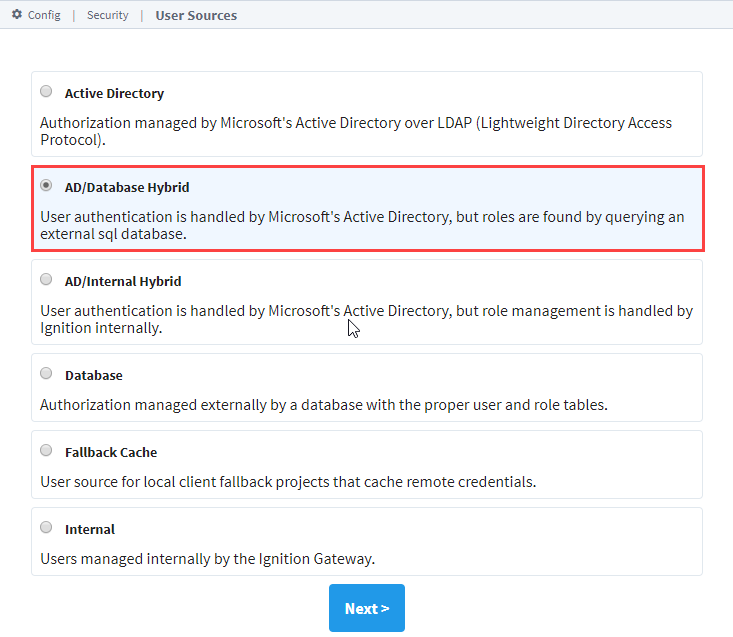
On the Gateway Webpage, under the Config tab, go to Security > Users, Roles. The Classic Authentication Strategy page will be displayed. Click the blue arrow, Create new User Source.
-
Choose the AD/Database Hybrid authentication type, and click Next.
 note
noteWhen using AD/Database Hybrid User Source, you may need to consult with your internal IT Department to get the required information to complete your user source setup.
-
The New User Source window will open. Some properties are optional depending on how you set up your profile. Details on the Main Properties can be found on the User Sources page. The Active Directory Properties and Database properties are listed in the tables below.
-
Click Create New User Source to save the new user source.
Active Directory Properties
| Name | Description |
|---|---|
| Domain | The Windows Domain your active Active Directory server is running on. If you aren't sure of your domain, ask your network administrator.Leave blank to set advanced properties manually. |
| Primary Domain Controller Host | The IP address or hostname of your primary domain controller. Example: "192.168.1.4" or "MainServer" |
| Primary Domain Controller Port | The port number for the primary domain controller's LDAP interface. |
| List Users from Active Directory | If true, Active Directory will be queried for the list of all users. If false, the database will be queried instead. Default is true. |
| Gateway Username | The login name for the Gateway to use when querying Active Directory. Used for retrieving the list of users and roles via LDAP. |
| Password | The password for the above username. |
| Password | Re-type password for verification. |
| SSO Enabled | Whether or not to use Single-Sign-On (SSO) to authenticate AD users. Note that projects must also have this option enabled for SSO to work. Default is false. Changed in 8.1.17 This setting was disabled and deprecated in 8.1.17 to protect against a potential security vulnerability. While the property is still visible, it cannot be enabled without setting a special system property. This is not recommended. Check out the Active Directory SSO Disabled for 8.1.17 & 7.9.20 article for more information. |
| SSO Domain | The domain that Windows users must match in order to use SSO. If blank, the main "Domain" property will be used. Not case-sensitive. |
Database Properties
| Name | Description |
|---|---|
| Database | Dropdown list. Choose the database connection this authentication profile will use. |
| User Properties Query | A query that returns the basic properties for a single user. Supported return columns are [username, firstname, lastname, schedule, language, notes]. |
| Role List Query | A query that returns all possible roles that any user could have. The role names must be returned in the first column of the query's results. |
| User's Roles Query | A query that returns all of the roles that the provided user belongs to. The roles must be strings (i.e., the role names), and must be in the first column of the query's results. The username will be inserted into this query as a parameter. |
| Contact Info Query | A query that returns all of the contact info for the user. The first column must be the contact type, the second column the contact value, and the third column the name of a schedule. Optional, may be blank. |
| Schedule Adjustment Query | A query that returns the upcoming schedule adjustments for the user. Columns must be Start(date), End(date), Available(boolean), Note(string). Optional, may be blank. |
| Extra Properties Query | A query that returns name, value pairs of extra properties for the user. Will be run with one parameter: the username. Optional, may be blank. |
| Find User Query | New in 8.1.6 A query that must return a row if a user with the given username exists. The query will be run as a prepared statement, so use question mark (?) to represent username. There must be at least one column: the username. Other columns are optional, supported columns are: [username, firstname, lastname, schedule, language, notes, badge].Example: SELECT username, firstname, lastname, schedule, FROM USERS WHERE username = ?When the User Source is paired with an Ignition Identity Provider, enabling this option can provide a modest performance improvement during session login. |
| List Users Query | A query that returns a row containing each username. Only used if "List Users from Active Directory" is false. There must be at least one column: the username. Other columns are optional, supported columns are: username, firstname, lastname, schedule, language, notes. |
| Badge Authentication Query | A query that must return a row if the given badge provided is valid. The query will be run as a prepared statement, so use question mark (?) to represent the badge. The returned row must contain the username. Example: SELECT username FROM USERS WHERE badge = ? |
Advanced Properties
The following table describes several configurable LDAP properties. See Microsoft's official documentation on LDAP Syntax Filters for more in-depth information about LDAP.
| Name | Description |
|---|---|
| Secondary Domain Controller Host | The IP address or hostname of your secondary domain controller (optional). Example: "192.168.1.5" or "BackupServer" |
| Secondary Domain Controller Port | The port number for the secondary domain controller's LDAP interface. Default: 389. |
| Read Timeout | The read timeout in milliseconds for LDAP operations. Default is 60,000. |
| Results Page Size | The number of entries returned per page of results in a query. Default is 1,000. |
| User Listing Base | The base folder to search for users under, such as DC=MyCompany,DC=com. The entire subtree under this folder will be searched using the User List Filter. Multiple subtrees can be specified by putting them in parenthesis, like so: (OU=Administrators,DC=MyCompany,DC=com)(OU=Operators,DC=MyCompany,DC=com) If you leave this blank the whole subtree of the domain controller will be searched. |
| User List Filter | The LDAP search filter used when querying for the list of all users. Should restrict the type to user. Default is (&(objectClass=user)(!(objectClass=computer))). |
| User Search Filter | The LDAP search filter to use to find a specific user. Use the placeholder 0 as a stand-in for the login name. Default is (&(objectClass=user)(sAMAccountName={0})). |
| User Name Attribute | The attribute on the User object to define the username. Default is sAMAccountName. |
| Username Prefix | This prefix will be prepended to the username before an Active Directory bind is attempted for authentication. |
| Username Suffix | This suffix will be appended to the username before an Active Directory bind is attempted for authentication. |
| Automatic Suffix | If this option is checked, and the suffix is left blank, then the suffix will automatically be assigned a value of @<domain>. Default is true. |
| Use prefix and suffix for Gateway username | New in 8.1.24 If this option is checked, the username prefix and suffix will be applied to the Gateway username before a bind is attempted. This option is checked by default. |
| Allow Anonymous | If enabled, authentication attempts with blank passwords will be passed through to LDAP, which may choose to accept them.Caution: It is highly recommended to disable this setting unless you know it is required. AD servers may allow logging in as any user with a blank password when Security Authentication is set to “None” or “Simple” (even if a provided username does not exist in AD), which is a major security risk. |
| Security Protocol | Auto or SSL. Default is Auto. |
| Security Authentication | This property specifies how usernames and passwords are used to bind to LDAP. The following options are available:
|
| Referral | New in 8.1.1 Specifies how referrals are to be processed. Possible options are:
|
SASL Properties
These settings are utilized when Security Authentication is set to SASL.
| Name | Description |
|---|---|
| Mechanism | An ordered list of space-separated mechanism names. The LDAP provider will use the first mechanism for which it finds an implementation. A blank value will leave this setting unspecified. Default is DIGEST-MD5 CRAM-MD5. |
| Realm | A realm defines the namespace from which the user is selected. A blank value will leave this setting unspecified. This setting will only be used by mechanisms which support it. Default is blank. |
| Quality of Protection | A comma-separated list of Quality-of-Protection (QoP) values, the order of which specifies the preference order. There are three well-known values: "auth" (authentication only), "auth-int" (authentication with integrity protection), and "auth-conf" (authentication with integrity and privacy protection). A blank value will leave this setting unspecified. This setting will only be used by mechanisms which support it. Default is auth-conf,auth-int,auth. |
| Protection Strength | A comma-separated list of privacy protection strength values, the order of which specifies the preference order. The three possible strength values are "low", "medium", and "high". A blank value will leave this setting unspecified. This setting will only be used by mechanisms which support it. Default is high,medium,low. |
| Mutual Authentication | Enable or disable mutual authentication. This setting will only be used by mechanisms which support it. Default is disabled. |
