Secure Disposal Guide
Environment Creation Considerations
A secure disposal plan begins at the creation of a new environment. Keeping detailed documentation of the services, locations, and where data is stored is vital to keeping information secure. In the event that the environment is removed, the proper documentation can then be referenced to ensure that all information about the project is purged and securely removed.
Ignition
Ignition is installed in the default directories for each operating system listed below. This directory includes Gateway configuration files, Ignition's internal database, project files, etc.
| System | Command |
|---|---|
| Windows | C:\Program Files\Inductive Automation\Ignition |
| Mac | /usr/local/ignition |
| Linux | /usr/local/bin/ignition |
| ARM (zip installation) | <installation path> |
Keep in mind that Ignition can be configured to take and store scheduled Gateway backups, and store them in any specified folder on the server, including to a mapped network drive. The folder location where automatic backups are stored can be set and found on the Gateway webpage, by navigating to Config > Gateway Settings > Schedules Backup Settings > Backup Folder.
The folder locations where Gateway backups are stored, and the Gateway backup files themselves should be included, and accounted for, in the disposal process. If they are not accounted for, then all Gateway, project, and tag data residing in the Gateway backup files could be left to be accessed, exploited, or restored by anyone with access to the directory.
For larger architectures that take advantage of remote backups with the Enterprise Administration Module (EAM), it is worth keeping track of where the agent backups are stored on the controller Gateway's filesystem. Please refer to Agent Task - Collect Backup for more information on the archive path.
Please note that the folder where Gateway backups are stored can be changed to multiple folders/directories over the lifetime of the environment. It is useful to run a search on the server's file system for any files with the Gateway backup file extension, .gwbk, during the disposal process of the environment.
Databases
Depending on the database service being installed the installation directory and data directory will be reflected in the respective manual. If the database is being installed on a separate environment take note of the location as well, as that system will need to be reviewed and purged in the event that the environment is removed.
I/O Peripheral Devices
Although Ignition does not store information to devices connected through the Gateway Network, such as PLCs, they should still be taken into careful consideration as a system that should be cleared when the system is no longer in use. Keeping record of the devices connected in the environment, their locations, and how to properly factory reset the device before removal is vital to ensuring that information does not end up in the wrong hands.
Prior to the creation of an environment, it's important to categorize how media will be removed in the event that the environment is modified or disposed. Systems in an environment may evolve over time and the filesystems and storage locations can change between upgrades. It is always important to document all modifications to the environment and update the media type and methods that will be taken in order to securely remove the environment. This will ensure that all media is accounted for when a user needs to remove media and that the proper sanitization decisions are followed.
Version Control
Version Control Systems (VCS) such as Git, Mercurial, or Subversion are powerful tools for managing changes to files over time. They allow tracking modifications, reverting to previous versions, and collaboration.
VCS can store a wealth of information about the Ignition Gateway, projects, tags, and more. This data can include code changes, configuration settings, and even user activity.
The repositories of these VCS are typically stored in specific locations on your system, network, or hosted in the cloud. It’s crucial to document these locations for future reference, especially if the environment is being decommissioned or removed.
Decommissioning Ignition Removal Steps
Properly uninstalling and removing Ignition guarantees that the configurations and data stored while the environment was active are completely removed and unrecoverable by unwanted parties.
Release License
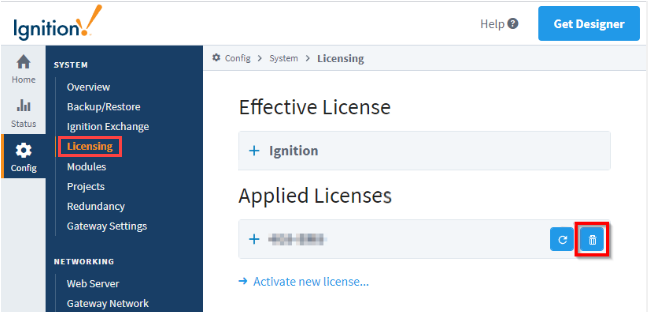
Before uninstalling Ignition, check and make sure the license has been deactivated. If not, navigate to Config > Licensing and select the trash icon to the right of the license key.
Uninstall Ignition
To uninstall Ignition, run the uninstaller file which can be found in the main Ignition installation directory.
Uninstalling Ignition will remove any projects or Gateway level configurations that were made. If there are projects or configurations that you would like to save, make sure to take a Gateway backup first.
| System | Command |
|---|---|
| Windows | C:\Program Files\Inductive Automation\Ignition\Uninstall.exe |
| Mac | /usr/local/ignition/Uninstall.app |
| Linux | '/usr/local/bin/ignition/Uninstall.run` |
| ARM (zip installation) | <installation path>/./ignition.sh remove |
Directory Removal
Once the uninstallation process has finished the Inductive Automation directory can be deleted. Please refer to the table below for the proper directory to remove.
Standard Removal
| System | Command |
|---|---|
| Windows | Remove-Item ‘C:\Program Files\Inductive Automation’ -Recurse |
| Mac | rm -r /usr/local/ignition |
| Linux | rm -r /usr/local/bin/ignition |
| ARM (zip installation) | rm -r <installation path> |
Secure Removal
Secure Removal is generally preferred over Standard Removal. This table provides examples of secure removal tools. Use discretion when downloading packages and running commands.
| System | Package | Command |
|---|---|---|
| Windows | Microsoft SDelete Package | sdelete -s -r ‘C:\Program Files\Inductive Automation’ |
| Mac | SRM (secure_deletion toolkit) | srm -r /usr/local/ignition |
| Linux | SRM (secure_deletion toolkit) | srm -r /usr/local/bin/ignition |
| ARM (zip installation)* | SRM (secure_deletion toolkit) | srm -r <installation path> |
| *Secure removal software depends on the Operating System running on the ARM device. |
Uninstalling and Removing Databases
Proper database removal is of utmost importance when ensuring secure data sanitization. Database services and file systems will remain on the installed system even when Ignition has been stopped, uninstalled, or removed. Therefore, databases used in conjunction with Ignition should be uninstalled and removed following the removal of Ignition. Due to the array of database management software that Ignition can connect to, please follow the uninstallation guidelines provided in the respective database documentation.
Media Sanitization
Once all conduits and services have been uninstalled and removed from the environment, media sanitization is recommended in order to render access to target data unrecoverable for a certain level of given effort. There are various standards that can be followed in order to sanitize storage devices, such as NIST Special Publication 800-88.
Proper removal requires understanding hard and soft copy media storage, and the types of sanitization. Understanding the type of data that is being sanitized can help you understand which of the following three methods is needed in order to sanitize the media device.
- Clear Method: This method is the simplest sanitization method. It typically involves using the Read and Write commands standards of the operating system to remove pointers to the addressable storage space on the media. This makes it difficult, but not impossible, for the media to be recovered. This may also include factory resets, which do not always guarantee the removal of sensitive information and simply delete the file pointers instead.
- Purge Method: This option takes the Clear method a step further by implementing an overwrite, cryptographic erase, or block erase to help in rendering the media unrecoverable. These methods rewrite over the stored information so not only the pointers to the files are removed, but the files are unrecoverable. Purge also includes degaussing as a step to render the storage media unrecoverable. This method uses a strong magnet to clear the memory from magnetic storage devices, though it is worth noting that this method does not work on non-magnetic storage and should not be solely relied on for flash storage devices.
- Destroy Method: This method is the most destructive of the three options and should be used for the most sensitive information. There is always a possibility that the information cleared or purged can be recovered, or that remnants of sensitive information was overlooked and not purged from the device. This method includes pulverizing, incinerating, or shredding techniques that make the media device data irretrievable even with the use of the latest laboratory techniques.
Sanitization of Storage Devices: